You signed in with another tab or window. Reload to refresh your session.You signed out in another tab or window. Reload to refresh your session.You switched accounts on another tab or window. Reload to refresh your session.Dismiss alert
Copy file name to clipboardExpand all lines: README.md
+6Lines changed: 6 additions & 0 deletions
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -15,6 +15,12 @@ Demo use-cases (optional):
15
15
16
16
[](https://www.youtube.com/watch?v=W-DyrsGRJeQ)
17
17
18
+
## Architecture
19
+
20
+

21
+
22
+
Each MCP client session gets its own isolated Sandbox CRD (Kata VM), with per-session gRPC connections, idle timeout cleanup, and max session limits. See [docs/grpc-sandbox-architecture.md](docs/grpc-sandbox-architecture.md) for details.
Copy file name to clipboardExpand all lines: docs/grpc-sandbox-architecture.md
+2-29Lines changed: 2 additions & 29 deletions
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -55,36 +55,9 @@ This document describes the gRPC-based sandbox execution architecture used in Pr
55
55
56
56
## Overview
57
57
58
-
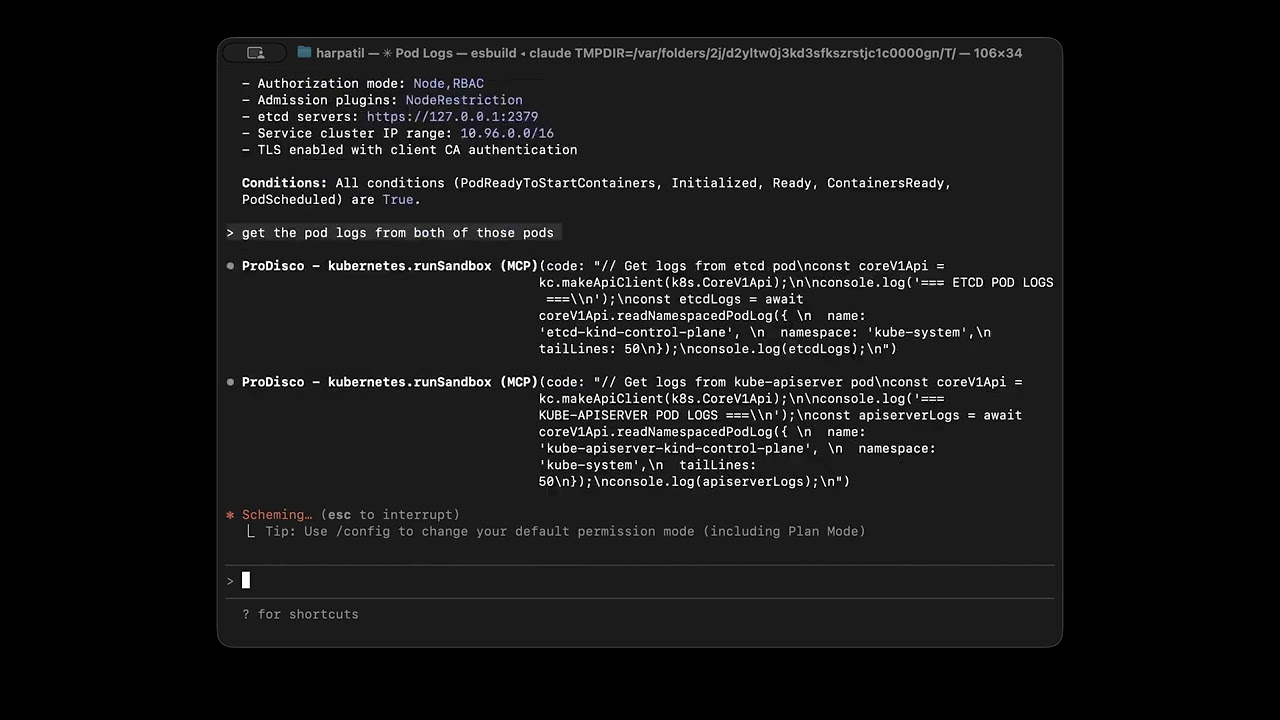
The sandbox system follows a client-server model inspired by Kubernetes' kubelet/containerd architecture:
58
+
The sandbox system follows a client-server model with per-session isolation. Each MCP client session gets its own Sandbox CRD, which provisions a dedicated pod and service:
Prometheus queries & metric discovery. PROMETHEUS_ENDPOINT env var is pre-configured in the sandbox.
25
+
Quick start: `const client = new PrometheusClient({ endpoint: process.env.PROMETHEUS_ENDPOINT });`
26
+
Range query: `client.executeRange('node_cpu_seconds_total', { start: new Date(Date.now() - 3600000), end: new Date(), step: '1m' })`
27
+
IMPORTANT: TimeRange.start/end must be Date objects or Unix timestamps in SECONDS (not milliseconds). Use `new Date()` or `Math.floor(Date.now()/1000)`.
28
+
Workflow: (1) create client with endpoint (2) client.execute('metric_name') for instant, client.executeRange() for time series.
29
+
- name: "@prodisco/loki-client"
30
+
description: |
31
+
Loki LogQL querying. LOKI_ENDPOINT env var is pre-configured. Auto-authenticates in Kubernetes using service account token.
32
+
Quick start: `const client = new LokiClient({ baseUrl: process.env.LOKI_ENDPOINT });`
33
+
Workflow: (1) create client (2) client.labels() and client.labelValues('namespace') to discover labels (3) client.queryRange('{namespace="default"}') to fetch logs.
34
+
- name: "simple-statistics"
35
+
description: "Statistical functions including mean, median, standard deviation, linear regression, and more."
36
+
---
7
37
apiVersion: v1
8
38
kind: ServiceAccount
9
39
metadata:
10
40
name: mcp-server
11
41
namespace: prodisco
12
42
---
43
+
# ServiceAccount for dynamically created sandbox pods
44
+
apiVersion: v1
45
+
kind: ServiceAccount
46
+
metadata:
47
+
name: sandbox-server
48
+
namespace: prodisco
49
+
---
50
+
# Read-only cluster access for MCP server and sandbox pods
13
51
apiVersion: rbac.authorization.k8s.io/v1
14
52
kind: ClusterRole
15
53
metadata:
@@ -36,6 +74,37 @@ roleRef:
36
74
apiGroup: rbac.authorization.k8s.io
37
75
kind: ClusterRole
38
76
name: mcp-server
77
+
subjects:
78
+
- kind: ServiceAccount
79
+
name: mcp-server
80
+
namespace: prodisco
81
+
- kind: ServiceAccount
82
+
name: sandbox-server
83
+
namespace: prodisco
84
+
---
85
+
# RBAC for MCP server to manage Sandbox CRDs (multi-sandbox mode)
0 commit comments